So this week there was a new Cumulative Update out that i wanted to test on a Storage Spaces Direct cluster. But as im using WSUS and VMM to patch my clusters i needed that patch to be in WSUS and it’s not. It will still take a few days before that patch get’s synced to WSUS, and i did not want to manualy update my nodes.
I googled and found a few posts about this but none that was good enough and it took me a while to find something relevant. So i decided i should share with you how you manually ad a Windows Update KB to WSUS.
The first thing you do is go to Microsoft Update Catalog and search for the update you need like 2020-10 windows server 2019 cumulative update

Then you get a list of updates, you can also search for Servicing Stack or other updates. Or just search on the KB you want.
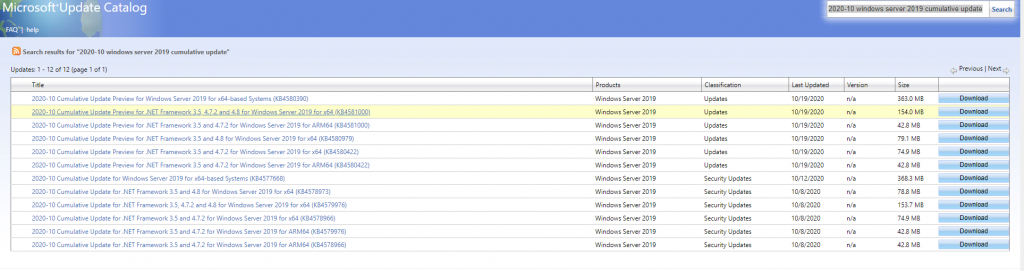
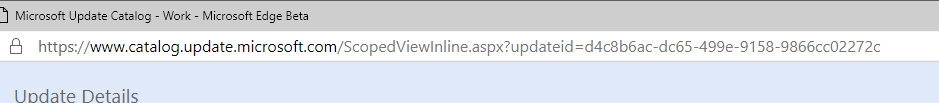
Download the KB’s you need and copy them to the Wsus server. Now we also need a GUID from the KB’s to import the updates. To get that click on the Update name on the left like 2020-10 Cumulative Update Preview for Windows Server 2019 for x64-based Systems (KB4580390)
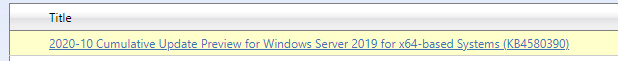
That will open a new browser window and in the link on top there is a GUID after updateid=.
Now let’s head back to the WSUS server, open up powershell ISE and run this command.
$KB = 'C:\temp\windows10.0-kb4580390-x64_743bc31f33bf399c7f15ab020df685780faf4cb5.msu'
$GUID = 'd4c8b6ac-dc65-499e-9158-9866cc02272c'
(Get-WsusServer).ImportUpdateFromCatalogSite($GUID,$KB)
Replace the file name and the GUID with what you got.
It might fail to run the commands. And it gives an error msg like this
Exception calling “ImportUpdateFromCatalogSite” with “2” argument(s): “The underlying connection was closed: An unexpected error occurred on a send.”
At line:1 char:1
+ (Get-WsusServer).ImportUpdateFromCatalogSite(‘f3af36f5-fdf4-f3be-f67f …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (:) [], MethodInvocationException
+ FullyQualifiedErrorId : WebException
This is due to TLS settings. Download IISCrypto and change settings to best practice and reboot WSUS server.
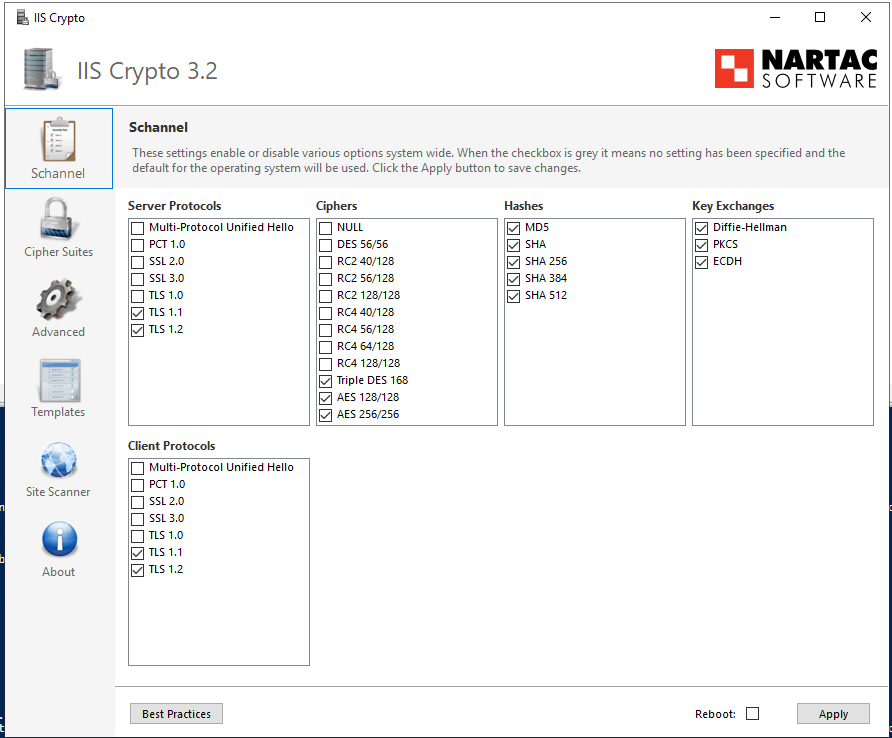
Also make sure POSH only supports TLS so run these commands at the same time before rebooting server.
[Net.ServicePointManager]::SecurityProtocol
#Set strong cryptography on 64 bit .Net Framework (version 4 and above)
Set-ItemProperty -Path 'HKLM:\SOFTWARE\Wow6432Node\Microsoft\.NetFramework\v4.0.30319' -Name 'SchUseStrongCrypto' -Value '1' -Type DWord
#set strong cryptography on 32 bit .Net Framework (version 4 and above)
Set-ItemProperty -Path 'HKLM:\SOFTWARE\Microsoft\.NetFramework\v4.0.30319' -Name 'SchUseStrongCrypto' -Value '1' -Type DWord
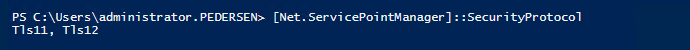
Restart PowerShell and check security protocols again:
[Net.ServicePointManager]::SecurityProtocol
POSH should show you only these security protocols.
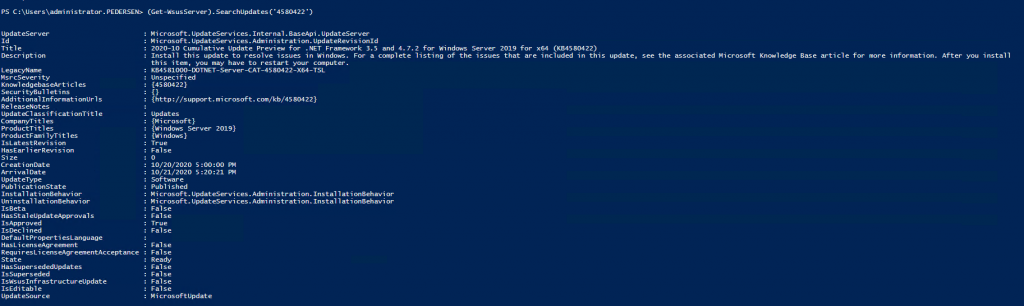
Once that is done you can run the script above again. And it will not error out. To verify that the update is added to WSUS run this command on wsus.
(Get-WsusServer).SearchUpdates('4580422')
It should give you an output like this
Thanks to Bronson at the slack channel for some input here on scripts and where to find the GUID 🙂